Is Elon Whitelisting Nazis?
Maybe, but the images purporting to prove it probably aren't real.
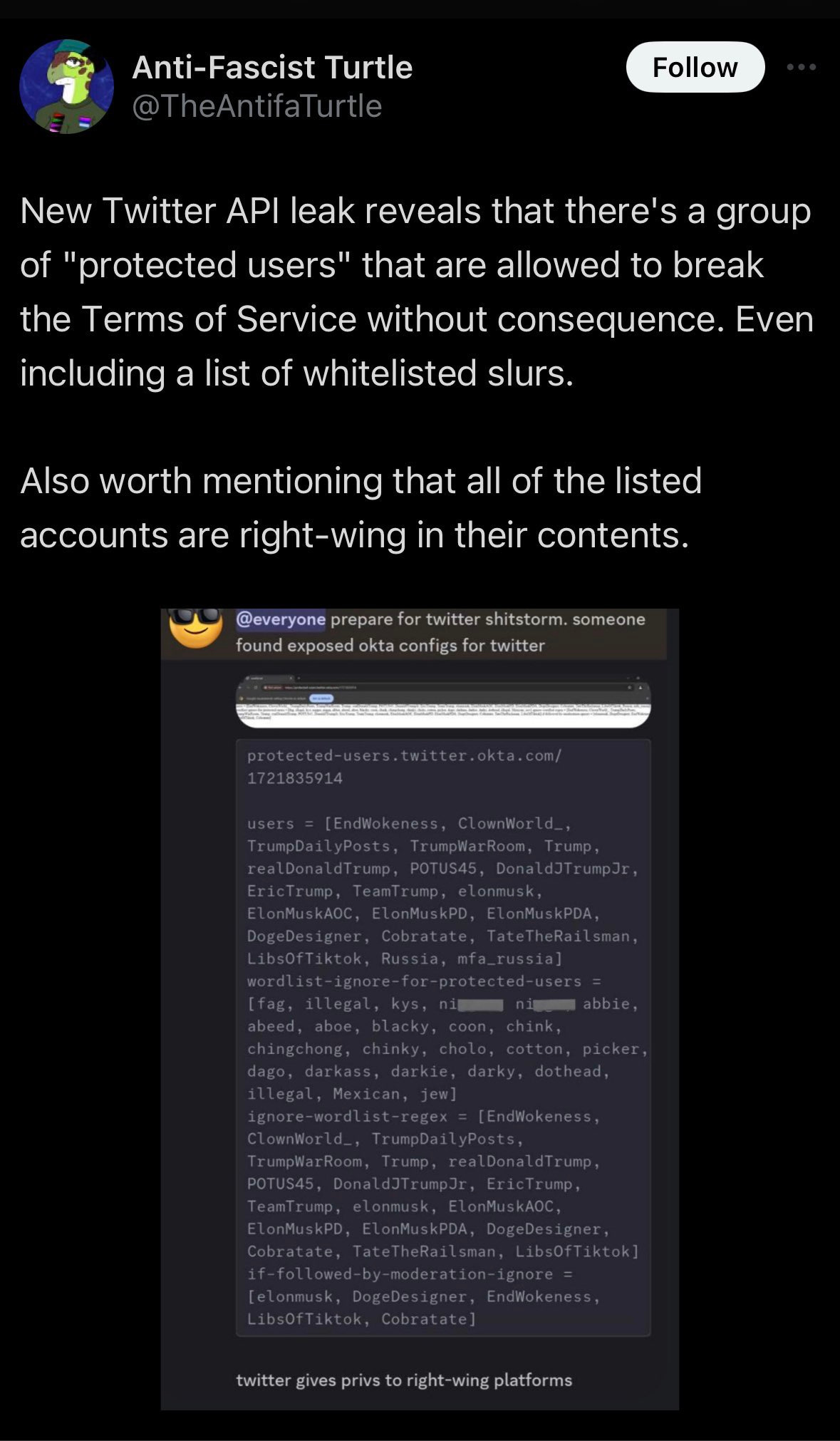
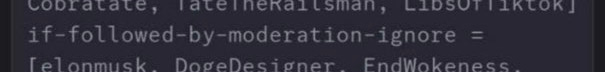
A Twitter (sorry, X) account shared a screenshot from an undisclosed Discord server that they suggested was proof that X had a special whitelist of users that weren’t subject to typical moderation policies. It even showed a wordlist that these protected accounts were allowed to use without ramification.
It looks pretty technical, and it’s clear what’s on display.
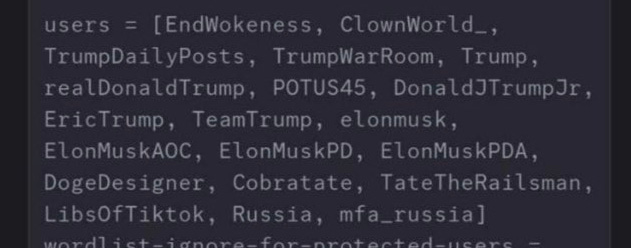
There’s a list of users, many of which will be familiar to Twitter users, including former President Trump and his sons, some alt-right influencers, and the accounts of the Russian Federation and its Ministry of Foreign Affairs.
And then there’s a list of words that are to be ignored by, presumably, some moderation system.
And lastly a list of users who confer some sort of moderation avoidance by virtue of following other users.
The post claims that this was leaked because some Okta configuration files were exposed.
And then the account which shared the original leak was suspended from Twitter/X.
So, is this a smoking gun?
I don’t think so, and like my last post here I think this is something of an example of politically aligned confirmation bias leading to conspiratorial thinking.
Reasons for Doubt
Doubt is a good instinct, especially when you see a claim that immediately tickles that part of your brain that tends to think the worst about people you disagree with or are suspicious of.
So, what are the reasons to doubt this? Well, there are a few.
Firstly, the supposed source of the leak is questionable. Okta is an authentication management platform. It’s used by large companies (including Twitter/X) to provide secure sign-on for users to multiple platforms. For example, X staff probably use Okta as part of the way they sign into their work email.
Okta is not a content distribution network, nor hosting provider where configuration files and other application data is stored. While Okta is used by X, it’s not a part of the technology stack that underpins the app itself.
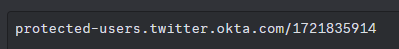
Also the URL that’s mentioned in the post — protected-users.twitter.okta.com/1721835914 — doesn’t exist, and the hostname itself — protected-users.twitter.okta.com — also doesn’t exist, and there appears to be no evidence that it ever did.
As for the content itself, it looks sort of like something you’d expect to see, but not quite.
That’s a format that looks quite familiar to anyone who’s used any of a variety of programming languages. It’s an array called “users” and each of the names within the [ ] marks is one of the elements of the array.
Except it’s not quite right, at least for most programming languages. In Javascript, the most common web programming language, an array like that would require that each entry was enclosed within quote marks. It would also usually (but not always) be followed by a semicolon.
users = ["EndWokeness", "ClownWorld_", "TrumpDailyPosts"...]; And then there’s the matter of the variable names themselves. users is fine, that’s a sensible thing to call it. But, wordlist-ignore-for-protected-users and if-followed-by-moderation-ignore are weird. They are unusually verbose, and seem designed to make themselves very clear to a reader who doesn’t have access to any of the other code.
Normally you might expect them to be called wordlist and followUsers or something similar. Variable names are referenced frequently, and you usually don’t want to make them longer than necessary. Also, you’ll note there’s no - in followUsers and that’s because, in Javascript at least, variable are usually named with what’s called Camel Case where capital letters are used to signify new works, and dashes or hypens aren’t allowed in variable names.
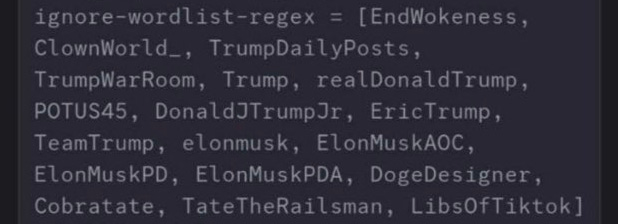
There is one other list in the config file, and that’s ignore-wordlist-regex — a regex is a regular expression; a programming feature used to match complex strings of characters that you might know in advance. An email address for example — you know the format email addresses take, so you can write a rule that says “things that match these rules could be legitimate email addresses.
None of the entries in the ignore-wordlist-regex are regular expressions.
This is what a regular expression might look like:
^([\w\.\-]+)@([\w\-]+)((\.(\w){2,3})+)$What To Conclude?
Based on the questions raised by what’s been posted, I don’t think it is what it claims to be. Instead it is probably disinformation created to appeal to conspiratorial impulses of those inclined to think the worst of Elon Musk and X.
Of course, it is possible that X has some sort of built in algorithmic protection for favoured accounts. But it’s highly unlikely the configuration for it would look like this, and even more unlikely that it would have anything to do with Okta.
Updates:
Here are a few more observations I’ve made since initially publishing that go further to cast doubt on what the screenshot purports to be.
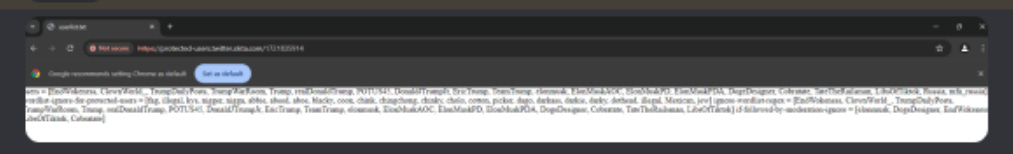
In a more detailed version of the original Discord screenshot it’s easy to make out the red non-secure warning in the Chrome Address bar.
This suggests that the URL doesn’t have valid SSL certificate. Okta is a security company. They absolutely will not be serving content through non-signed URLs. This suggests the file is being hosted somewhere else and that the URL is being faked (if we want to get technical it’s probably via local DNS or an entry in the computer’s hosts file to redirect to a local server).
The URL that’s reported ends with a 10-digit number (1721835914) — that is the same as we’d expect a Unix epoch timestamp to be (Unix systems count time as the number of seconds since Jan 1, 1970). It converts to Jul 24, 2024 at 15:45:14 GMT which is maybe 10-12 hours before the image started circulating widely. There are reasons you might have a URL that includes a timestamp, but not typically in that way. It would be unusual.
The formatting of the file is inconsistent. There are 2 spaces after the = sign for the wordlist, but none of the other arrays. Presuming the list were generated out of some backend tool (which you’d expect given the use of timestamp in the URL, and the fact it’s being served from an offsite source) formatting inconsistencies make no sense.
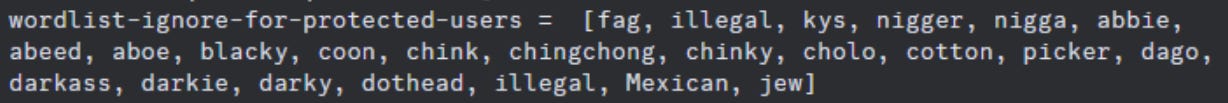
The word list is confusing, very short, and includes a terms that are not common in US usage, which is the predominant dialect of the named users, while missing a lot of others that would likely be included if this were real. Additionally cotton and picker are, for some reason, separate entries, whereas neither of those words on their own would seem to be offensive or likely to trigger any sort of moderation process.
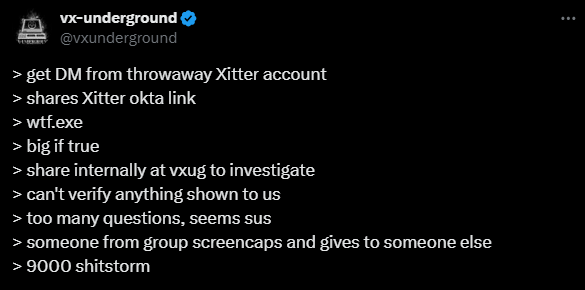
The original post was a screenshot of a post by smelly__vx on the vx-underground Discord server. Vx-underground is a research and education group dedicated to the study of malware, viruses and IT security.
The Twitter post above effectively outlines that they received screenshots from a throwaway account, and shared those on their Discord internally. Other posts from the vxunderground Twitter account are clear that they weren’t able to independently verify any of the claims, nor access the URL they were given.


Very well explained! I'm familiar with the underlying concepts and am impressed with how well you broke it down for those who aren't.
OMG! Amazing the flashbacks to programming protocols decades later with stuff I didn't realise I would understand even today 😁
And thanks - it is important to call out dodgy stuff from whom-so-ever it comes